Security
Zoom Vulnerabilities with Patrick Wardle

Zoom video chat has become an indispensable part of our lives. In a crowded market of video conferencing apps, Zoom managed to build a product that performs better than the competition,
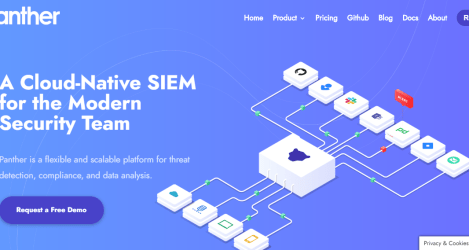
Cloud Log Analysis with Jack Naglieri

Large software companies have lots of users, and the activity from those users results in high volumes of traffic. These companies also have a large surface area across the enterprise.
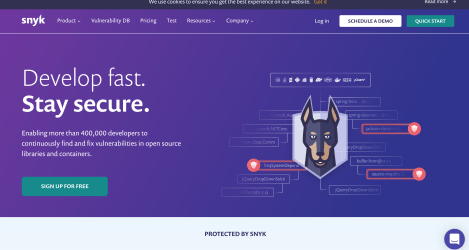
Snyk: Open Source Security with Guy Podjarny
The software supply chain includes cloud infrastructure, on-prem proprietary solutions, APIs, programming languages, networking products, and open source software. Each of these
Security Monitoring with Jeff Williams

The modern software supply chain contains many different points of distribution: JavaScript frameworks, npm modules, Docker containers, open source repositories, cloud providers, on-prem
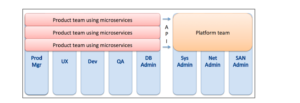
Container Platform Security with Maya Kaczorowski
A Kubernetes instance occupies a wide footprint of multiple servers, creating an appealing target to an attacker, due to its access to a large pool of compute resources. A common attack